Room Link: Operation Slither Room Link
let’s see what info do we have here.
so the name of the leader here is:
@v3n0mbyt3_
On a simple google search we can see the X account under the name.
but we have to find another social media where @v3n0mbyt3_ is used as a username.
just scroll down more and you will see a new social media platform from meta.
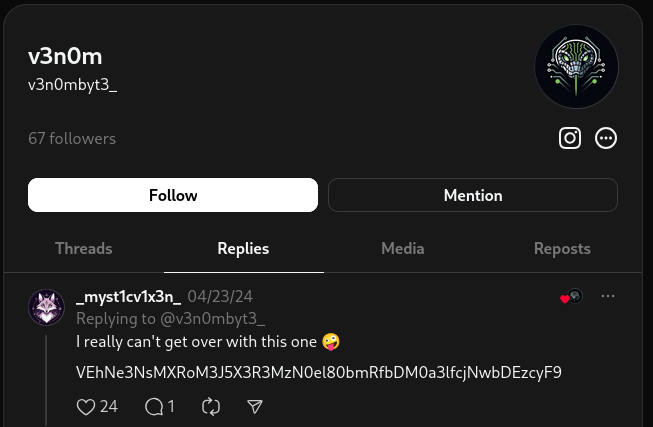
going to the replies we can see there is a base64 encoded text here
let’s decode it using terminal.
echo "VEhNe3NsMXRoM3J5X3R3MzN0el80bmRfbDM0a3lfcjNwbDEzcyF9" | base64 -d
and we got the flag.
Task 2
we can see from the Task 1 replies,
The account talked to the leader.
let’s check the user’s Instagram.

we can see the sound cloud link here. let’s visit
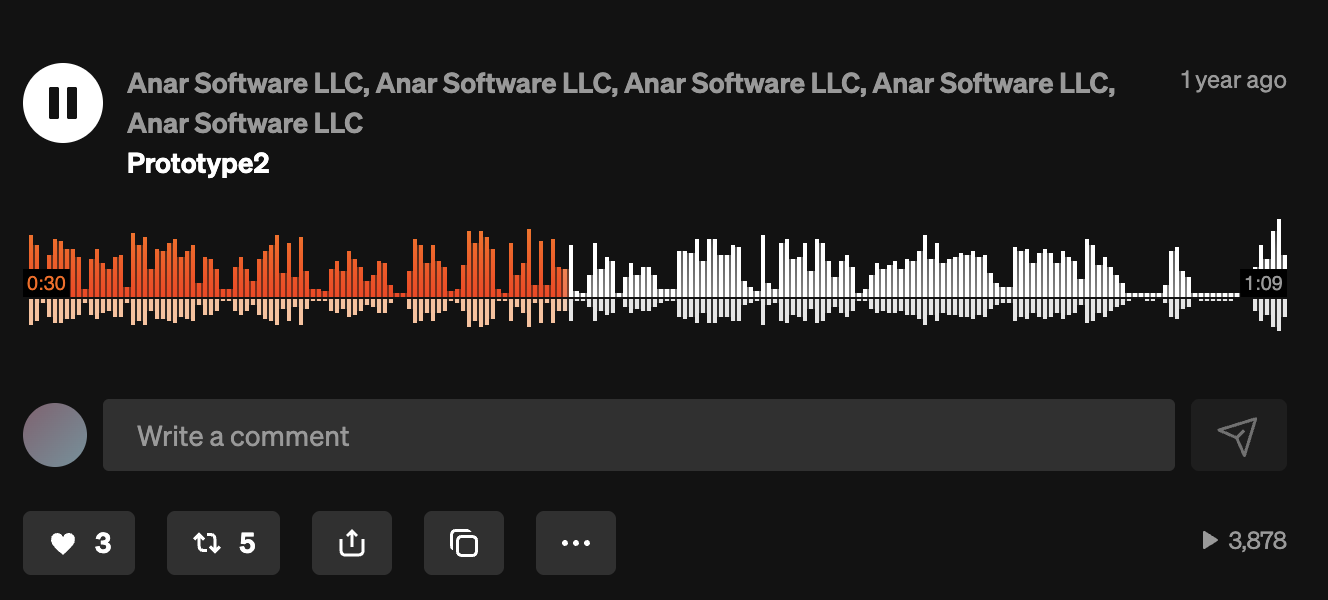
this audio is the what we needed. visit it and you will find another base64 encoded text
echo "VEhNe3MwY20xbnRfMDBwczNjX2Yxbmczcl9tMXNjbDFja30=" | base64 -d
and we got the flag.
Task 3
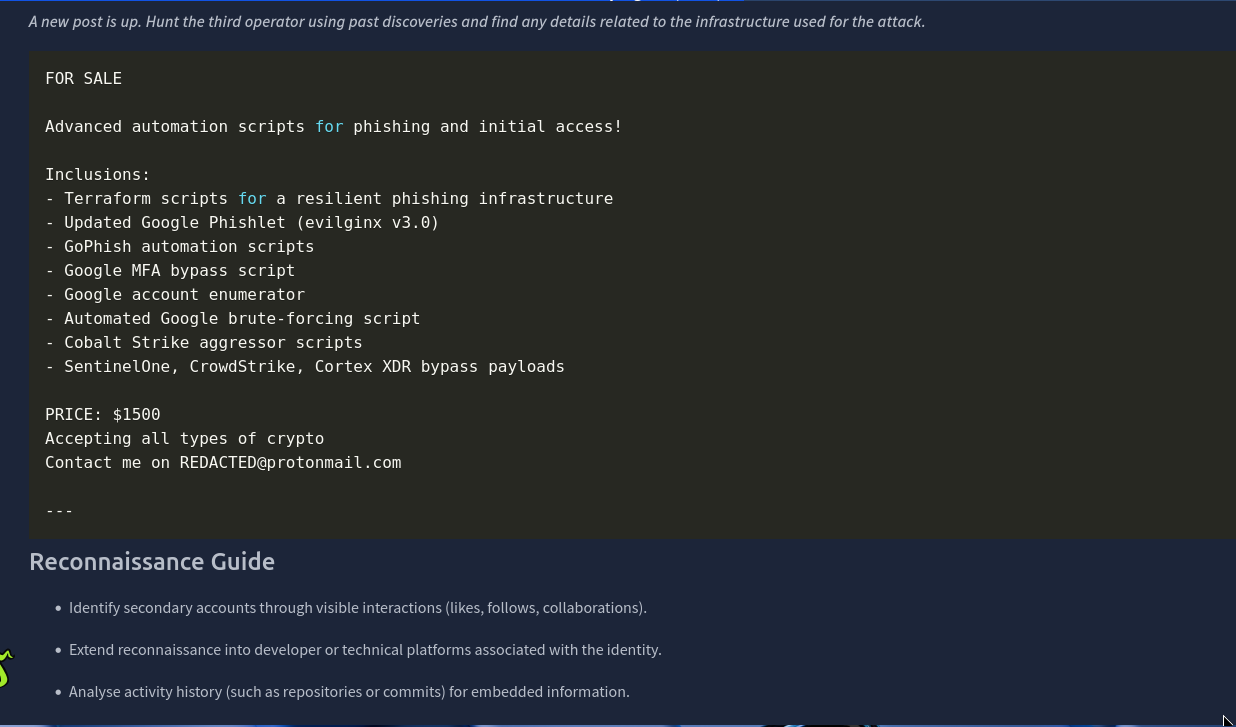
i think we can identify the suspicious follower here.
we got our first flag here.
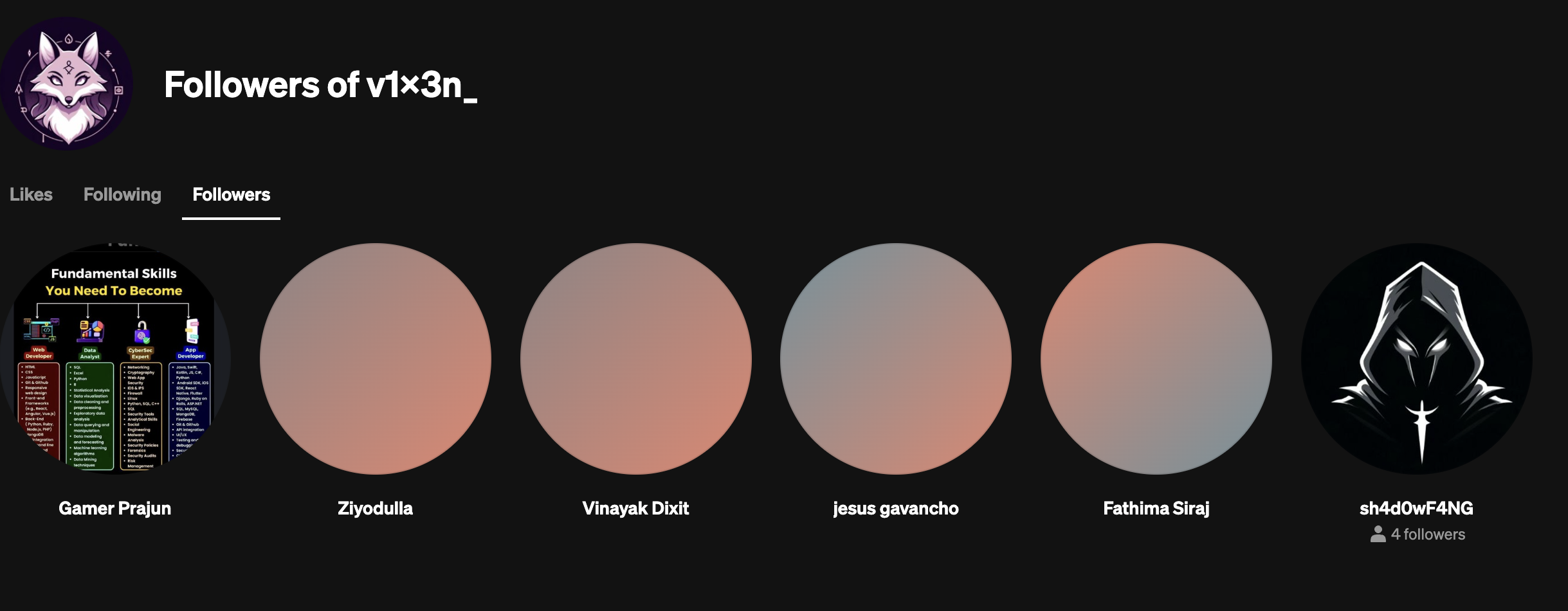
we can identify the answer for second question with the 3rd point in recon guide. or even a simple google search for username will also do.
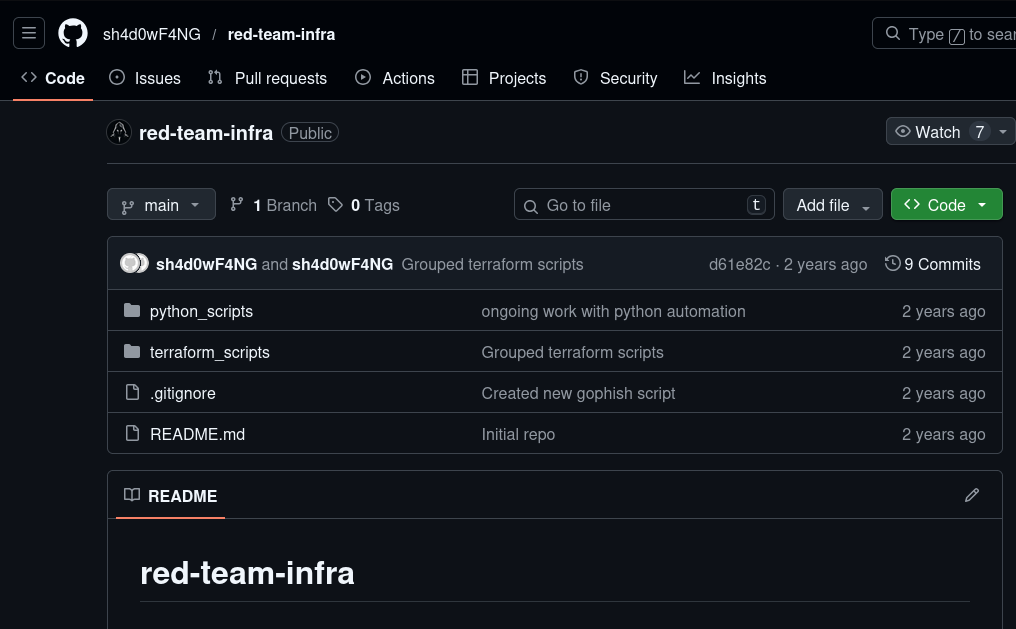
we found this GitHub repo here
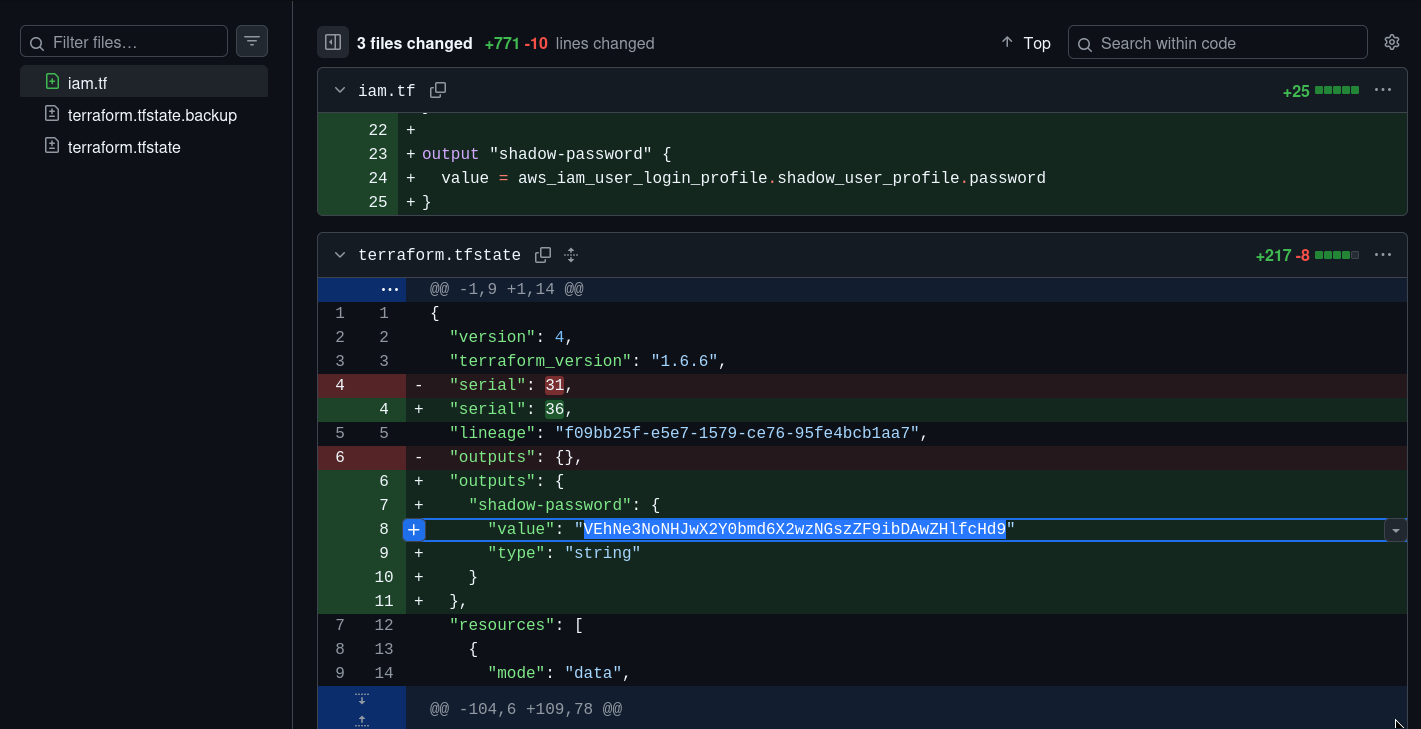
under commits you can find this file which has shadow password in the form of base64.
echo "VEhNe3NoNHJwX2Y0bmd6X2wzNGszZF9ibDAwZHlfcHd9" | base64 -d
BOOM! we got our flag here.
